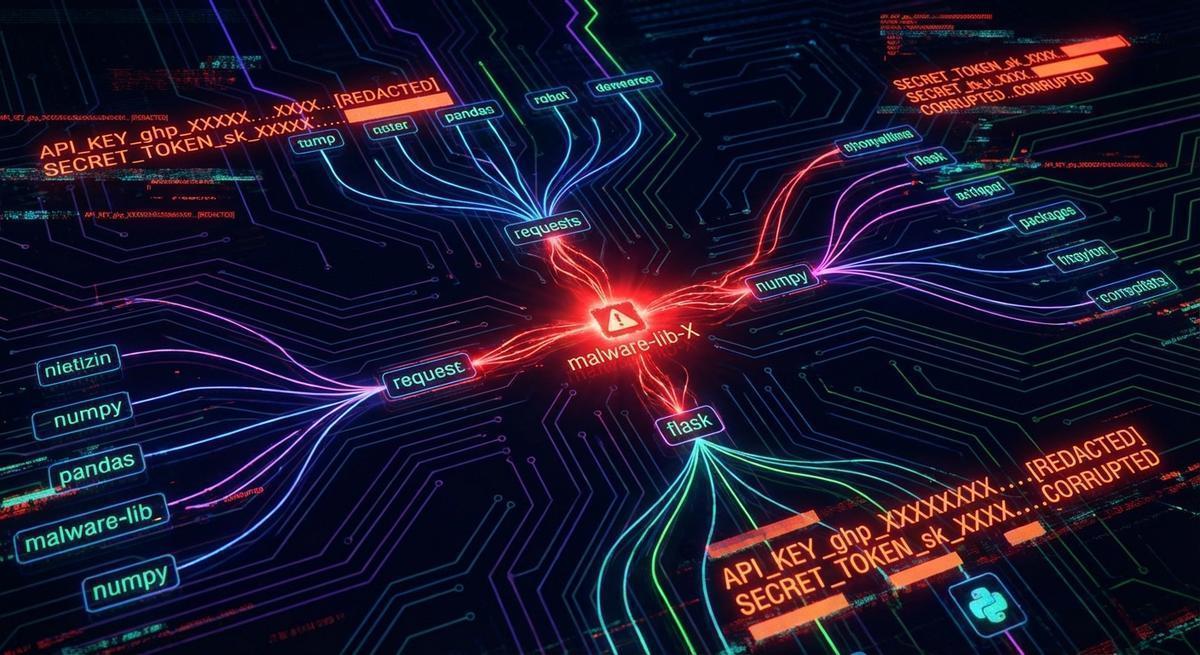
If you installed LiteLLM 1.82.7 or 1.82.8, your credentials are already gone. The question isn’t whether you were affected. It’s what the attacker can do with what they took.
Here’s what the malicious package did: it used a .pth file injection that runs at Python interpreter startup, before your code does anything. Every machine with those versions installed had its environment drained the moment any Python process launched. SSH keys, AWS credentials, GCP and Azure tokens, OpenAI API keys, database passwords, shell history. The r/LocalLLaMA thread has the full technical breakdown. The exfiltration completed in under an hour.
The standard advice is to rotate everything immediately. That’s not wrong, but it misses the actual problem. Rotation is a response. This attack operated on a timeline that makes response nearly irrelevant. By the time most teams detect a compromised package, open their cloud consoles, and revoke the old credentials, the data is already in the attacker’s bucket.
The real problem: your .env file had live credentials in it. Anyone who reads that file gets a ready-to-use toolkit. That’s what this post is about, and how to fix it before the next one lands.
Why “Just Rotate Your Keys” Doesn’t Help Here
The standard advice after any credential leak is to rotate everything. It’s not wrong, exactly. But it misses the point when you’re talking about supply chain attacks, and it does nothing to protect you from the next one.
Here’s the math: the LiteLLM packages were live for less than an hour. How fast do you rotate? How fast do you even know something needs rotating? Most teams don’t have sub-hour detection on compromised packages. By the time you’ve identified the issue, opened your cloud console, revoked the old keys, and generated new ones, the attacker already has what they came for. Your data is in their bucket. Your API usage is already running up their tab.
Rotation is a response. Supply chain attacks operate on a timeline that makes response nearly irrelevant. The gap between “package published” and “you find out” is measured in hours at best, days at worst. An exfiltration that completes in 45 minutes doesn’t care that you rotated 6 hours later.
What you actually need is a setup where the credential that gets stolen has no standalone value.
The Real Problem: Your .env Has Live Credentials
Open your .env file. If it looks like this, you have a problem:
OPENAI_API_KEY=sk-proj-abc123realkey...
ANTHROPIC_API_KEY=sk-ant-api03-realkey...
AWS_ACCESS_KEY_ID=AKIA...realkey
AWS_SECRET_ACCESS_KEY=realsecret...
DATABASE_URL=postgresql://user:realpassword@host/dbThat’s the file a supply chain attack reads. Every value there is a live credential. Anyone with those strings can make authenticated API calls, spin up AWS resources, bill you into oblivion, or read your production database. The malicious LiteLLM package didn’t need to crack anything. It just read the file and sent it over the wire.
This pattern, live credentials sitting in .env, is completely normal. It’s how most Python AI projects are set up. It’s also exactly why supply chain attacks against the Python ecosystem are so effective. The payload writes itself.
What Changes With Phantom Tokens
The phantom token pattern changes what’s in your .env. Instead of live credentials, you store fake placeholder tokens. They look plausible, they follow the right format, but they have no standalone value. They only work if they pass through a local proxy that knows the real credentials and performs the swap at runtime.
Your .env becomes:
OPENAI_API_KEY=phantom-abc123
OPENAI_BASE_URL=http://localhost:8900/openai
ANTHROPIC_API_KEY=phantom-def456
ANTHROPIC_BASE_URL=http://localhost:8900/anthropicNow when a malicious package reads OPENAI_API_KEY, it gets phantom-abc123. That string fails on any direct OpenAI request. It can’t make API calls. It can’t bill anyone. There’s nothing to rotate because the credential that got stolen was never real.
Your application code doesn’t change. The SDK still reads OPENAI_API_KEY from the environment. The SDK still sends requests to OPENAI_BASE_URL. The proxy running at localhost:8900 intercepts those requests, swaps the phantom token for the real credential, and forwards the call to OpenAI. To your code, everything looks identical. The logs look identical. The latency is negligible.
Make your .env worthless to attackers
Phantom tokens replace live credentials in your environment files. A supply chain attack reads noise instead of your real keys. Set up takes under 10 minutes.
No credit card required
How to Set This Up Locally
You need API Stronghold running locally. Once it’s up, the proxy handles the token swap at runtime, and your project directory holds nothing sensitive.
Configure your project’s .env:
OPENAI_API_KEY=phantom-dev-openai
OPENAI_BASE_URL=http://localhost:8900/openai
ANTHROPIC_API_KEY=phantom-dev-anthropic
ANTHROPIC_BASE_URL=http://localhost:8900/anthropicThe real credentials live in the AS configuration, not in your project directory. Not in your repo. Not in any file that a malicious package is going to find when it scans for OPENAI_API_KEY.
Any SDK that respects OPENAI_BASE_URL routes through the proxy automatically. The OpenAI Python SDK does. LiteLLM does. LangChain does. Most agent frameworks do. You set the base URL once, and it works without further changes to your code.
The phantom token is sent with each request. The proxy validates it against a known list, then attaches the actual credential before forwarding. If someone takes that phantom token and tries to use it directly against OpenAI, the request fails. OpenAI has never seen that token. It means nothing outside the proxy.
Production Works the Same Way
In production, the proxy runs server-side instead of on your laptop. Your agents and applications point at it the same way they pointed at your local instance.
OPENAI_API_KEY=phantom-prod-openai-agent-1
OPENAI_BASE_URL=https://proxy.yourcompany.com/openaiThe real OpenAI key lives in the proxy’s configuration, behind your infrastructure. Agents get phantom tokens scoped to their specific role or service. You can revoke a single agent’s access without touching the underlying API key or affecting other services. You get per-token request logs, which means you have attribution on every call.
Supply chain attack hits your build system and reads environment variables? The attacker gets a phantom token with no standalone value and a URL pointing at a proxy they can’t authenticate to. They can’t use either without also compromising your proxy infrastructure, which is a much harder target than a flat .env file.
What the Attacker Gets, With and Without This Setup
Without phantom tokens, a supply chain attack that reads your .env gets a ready-to-use toolkit:
- A working OpenAI API key. Immediately usable to run inference, rack up bills, or exfiltrate your prompt history.
- A working Anthropic key. Same deal.
- AWS access key and secret. Full account access depending on your IAM configuration.
- Your database connection string with credentials embedded. Direct read access to production data.
With phantom tokens, the same attack reads your .env and gets:
phantom-abc123. Not an OpenAI key. Fails immediately on any direct OpenAI request.- A proxy URL pointing at your infrastructure. Requires network access and its own authentication.
- No AWS credentials. No database password. Those don’t live in
.envanymore.
The attack still happened. The exfiltration still happened. But the payload is noise.
This is the difference between a security incident that requires immediate credential rotation across every service, frantic Slack messages at 2am, and an unknown blast radius, versus a security incident where you update your phantom token list, add an alert, and move on.
The Actual Takeaway
Supply chain attacks are not going away. The LiteLLM incident was not a one-off. Attackers compromise popular packages because the math works in their favor. One infected package, millions of installs, millions of environments. The development ecosystem runs on transitive dependencies. You cannot audit all of them.
You can’t catch a malicious package in the 45 minutes it’s live on PyPI. You can’t rotate fast enough to outrun exfiltration that completes before you even know to look.
What you can do is make your environment files worthless to anyone who reads them. Phantom tokens don’t require you to trust your dependency tree. They assume the tree is already compromised and design around that assumption. Your code works the same. Your .env file becomes noise to any attacker who grabs it.
That’s a setup worth having before the next one lands.
Your .env is the attack surface. Stop treating it like a secret store.
API Stronghold keeps real credentials out of your environment files. Phantom tokens, zero-knowledge encryption, works with any LLM SDK.
No credit card required