
AI Agent Blast Radius: What Happens When One Key Leaks
Most teams can't answer a basic question: if this API key leaks, how much damage can it do? We built a blast radius report to find out. The answer was worse than expected.
Practical security insights and product updates from the team building safer, simpler key management for modern APIs.

Most teams can't answer a basic question: if this API key leaks, how much damage can it do? We built a blast radius report to find out. The answer was worse than expected.

Every AI security layer has holes. The swiss cheese model shows why stacking imperfect defenses is the only strategy that works for AI agent pipelines.
Multi-agent AI pipelines have a supply chain problem. See 4 real attack patterns, including MCP skill trojans and orchestrator trust exploitation, plus 5 code-level defenses.

10 documented prompt injection attacks that hit production AI systems, plus 5 concrete defense steps with code you can copy. Each attack shows exactly how credentials get stolen.

Security researchers found 21,000 exposed OpenClaw instances in two weeks. Here's why agent tokens leak and how scoped secrets contain the damage.
Most teams still pass .env files around like contraband. The API Stronghold CLI generates them from your vault in seconds, remembers your preferences per project, and syncs secrets to GitHub, Vercel, and Cloudflare.

135,000 exposed OpenClaw instances, 824+ malicious skills, and a CVSS 8.8 RCE in 2026. Here's what went wrong and how to stop your API keys from being the next casualty.

Crypto AI agents execute trades at machine speed with no human confirmation. When the API key leaks, the damage happens in minutes. Here's how to scope credentials so a theft can't drain your account.

Share secrets with configurable view limits, IP and country restrictions, longer expiration windows, and email notifications before expiry. Four new features for secure credential sharing.
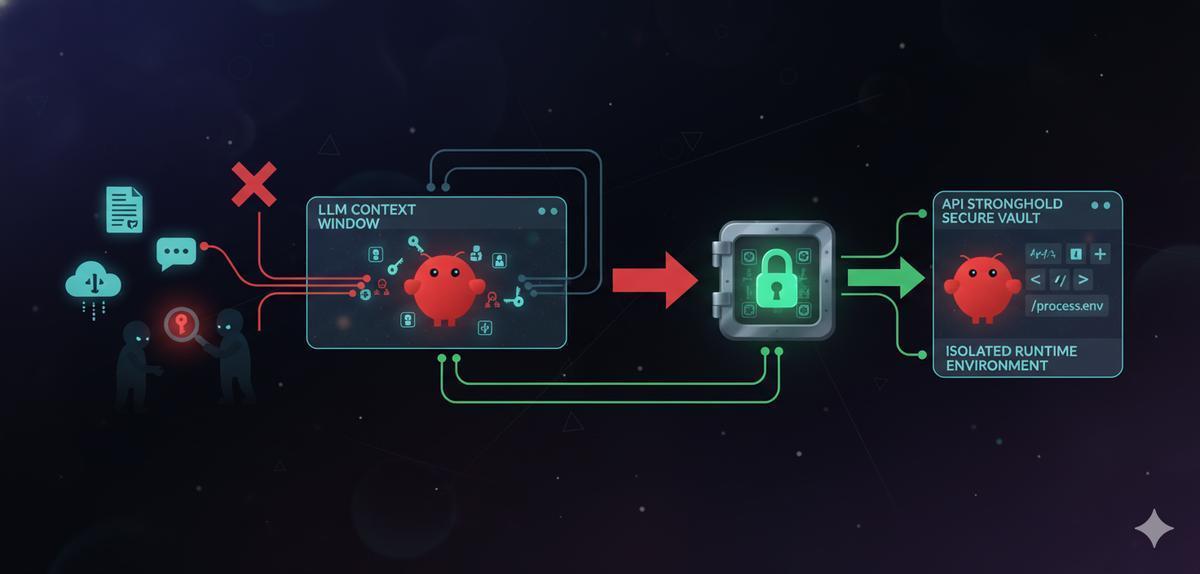
7% of OpenClaw skills expose API keys through the LLM context window. Isolate your credentials with scoped secrets so keys never touch the model.