
Sandboxing Your AI Agent Doesn't Fix the Credential Problem
Every sandbox tool assumes the agent already has your real API keys. That's the problem, not the solution.
Practical security insights and product updates from the team building safer, simpler key management for modern APIs.

MCP skill marketplaces have the same supply chain problems as npm, except the blast radius is your AI agent's full context window. Here are 5 vulnerabilities with code fixes you can deploy today.
Read →
Your secrets management provider can read your plaintext API keys. Here's how zero-knowledge encryption works, what it changes for compliance, and when enterprise teams actually need it.
Read →
API keys shared through Slack, email, and spreadsheets waste developer hours and create security gaps. Here's what insecure credential sharing actually costs your team, and how to fix it with automated, encrypted sharing.
Read →
Every sandbox tool assumes the agent already has your real API keys. That's the problem, not the solution.

GitHub Copilot uses all open IDE files as context, including your secrets. Here's what gets transmitted, what GitHub's policy covers, and how to lock it down.
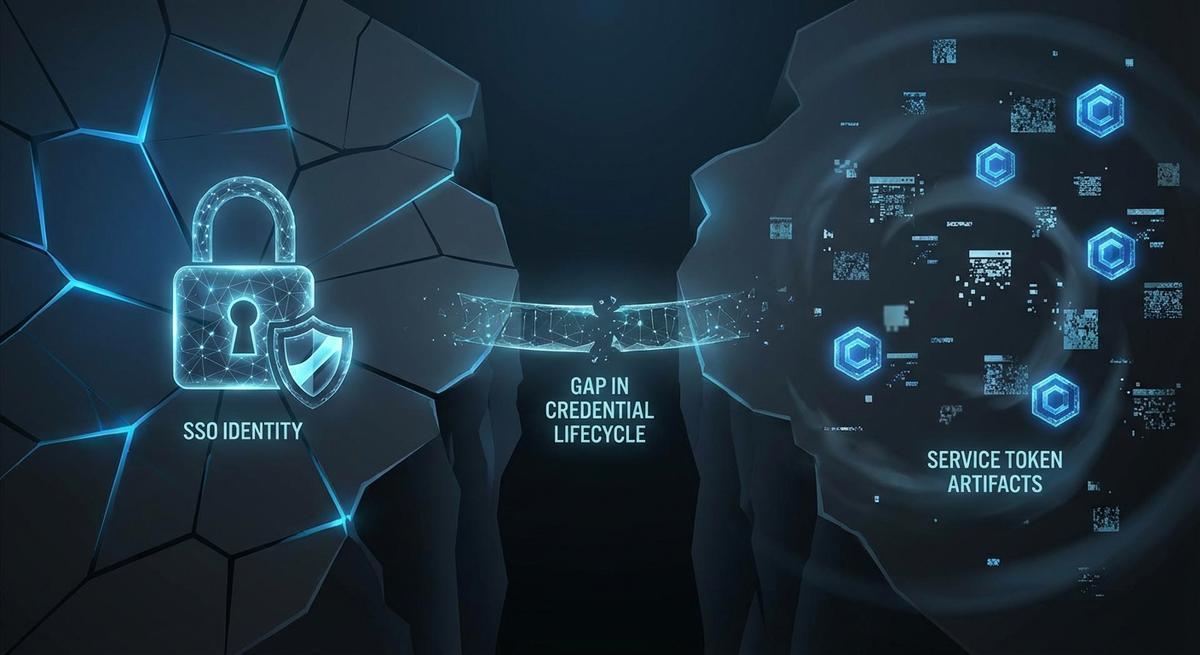
Offboarding in Okta stops logins. It leaves GitHub PATs, AWS IAM keys, and OAuth grants running. Here's the exact checklist to kill all of it.

Axios fell to a persistent maintainer token that leaked and enabled credential theft. When attackers move in minutes and rotation takes days, expiration is the only math that works.

Terminating an employee triggers an SSO deactivation and a laptop wipe. It rarely triggers a credential audit. Here's the gap that lets ex-employee API keys persist for months.

AI agents execute across tools with no memory of what came before. Your logs capture 200 OKs, not consequences. Here's how to build workflow-level audit trails that actually show what happened.
TeamPCP backdoored telnyx 4.87.1 and LiteLLM using the same RSA key infrastructure, targeting environment variables both times. Until you stop storing live credentials in .env, rotation is just cleanup.

GitHub Copilot's new training policy starts April 24. The risk isn't just code, it's the secrets in your open files. Here's a 5-minute checklist to protect your API keys.

Rotation assumes keys are valid until scheduled. Expiration assumes they're dangerous from day one. One of those assumptions matches how attackers actually behave.

If your AI agent traces include tool-call HTTP bodies - and they do by default in LangChain, LlamaIndex, and most OpenTelemetry setups - every API key your agent touched is sitting in your observability stack.