
MCPGuard vs API Stronghold: Two Layers of MCP Security
MCPGuard secures MCP traffic. API Stronghold secures the credentials inside it. Here's the difference, when you need each, and why most teams need both.
Practical security insights and product updates from the team building safer, simpler key management for modern APIs.

MCP skill marketplaces have the same supply chain problems as npm, except the blast radius is your AI agent's full context window. Here are 5 vulnerabilities with code fixes you can deploy today.
Read →
Your secrets management provider can read your plaintext API keys. Here's how zero-knowledge encryption works, what it changes for compliance, and when enterprise teams actually need it.
Read →
API keys shared through Slack, email, and spreadsheets waste developer hours and create security gaps. Here's what insecure credential sharing actually costs your team, and how to fix it with automated, encrypted sharing.
Read →
MCPGuard secures MCP traffic. API Stronghold secures the credentials inside it. Here's the difference, when you need each, and why most teams need both.

When multiple AI agents share the same credentials, one compromised agent exposes everything. Here's how to give each agent its own isolated session with the exact keys it needs.

CNCERT flagged prompt injection in AI agents as a national security risk. The Telegram link preview exfiltration technique is real. Here's how a credential proxy makes it structurally impossible.
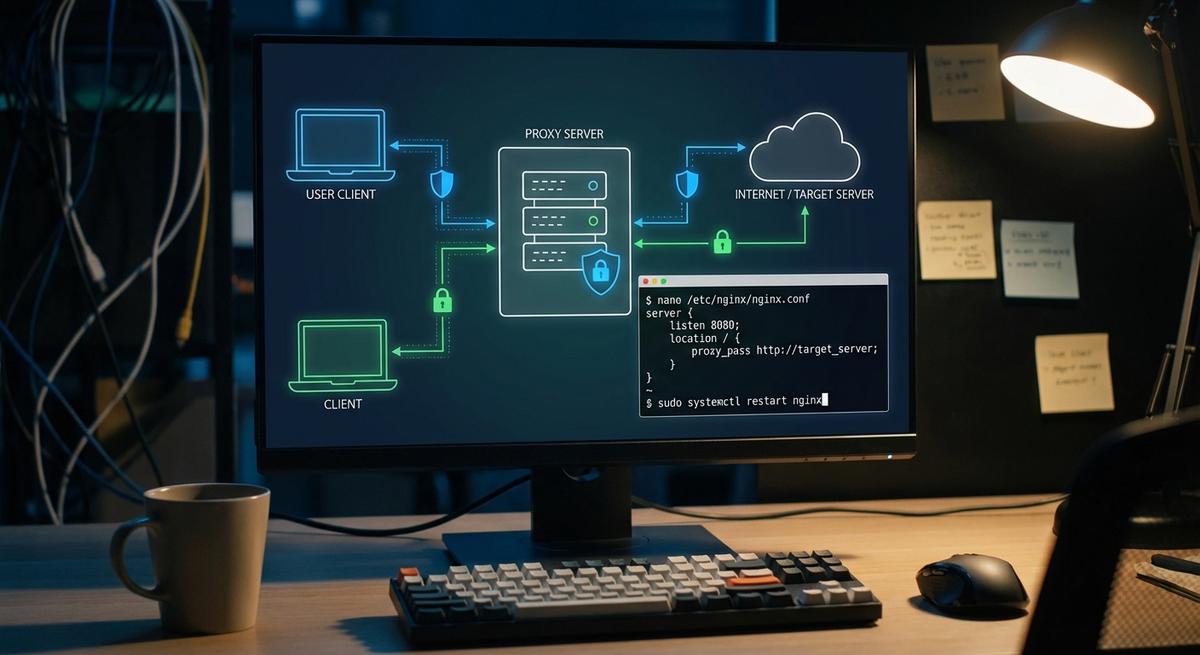
Run API Stronghold as a credential proxy for OpenClaw so agents never hold real API keys. Fake keys in, real credentials injected at the proxy, nothing reaches the LLM context window.

PII breaches get the headlines and the regulatory fines. Credential leaks get the access. Here's why an exposed API key is often more dangerous than leaked personal data, and what you can do about it.

AI agents accumulate API keys fast. Learn how credential sprawl happens, why it's a security crisis, and how to audit and shrink your agent's key footprint.

A practical pre-deployment security checklist for AI agents. Catch credential leaks, over-permissioned keys, and blast radius risks before they hit production.

Stop hardcoding API keys into MCP servers. Here's the register→scope→issue→validate→expire pattern with real endpoints platform engineers can deploy today.

Most teams can't answer a basic question: if this API key leaks, how much damage can it do? We built a blast radius report to find out. The answer was worse than expected.

Rotating API keys every 90 days sounds responsible. Attackers exploit leaked keys in minutes. Here's why rotation is a lagging control and what actually stops credential-based breaches.