6 Fields Every AI Agent Audit Log Needs (Most Skip 4)
Most agent logs capture what happened, not who triggered it or why. Here are the 6 fields every AI agent audit trail needs for real compliance.
Practical security insights and product updates from the team building safer, simpler key management for modern APIs.
Most agent logs capture what happened, not who triggered it or why. Here are the 6 fields every AI agent audit trail needs for real compliance.

Real AI agent incidents share one root cause teams keep missing: credential architecture. Here's what those post-mortems get wrong every time.
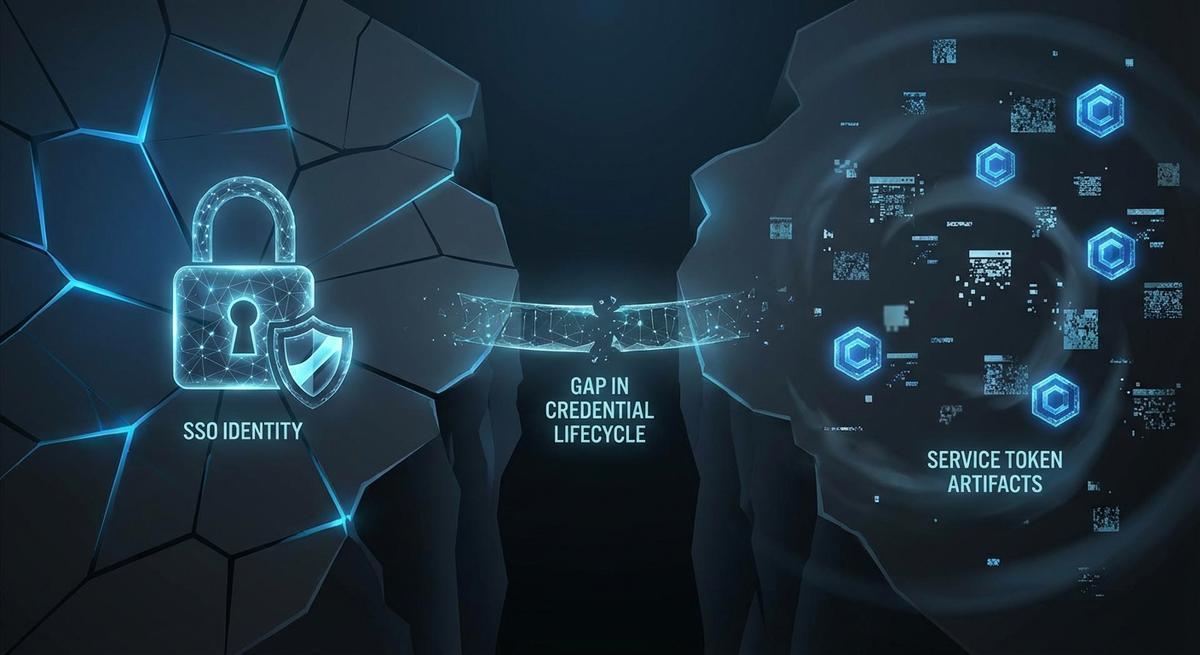
Offboarding in Okta stops logins. It leaves GitHub PATs, AWS IAM keys, and OAuth grants running. Here's the exact checklist to kill all of it.

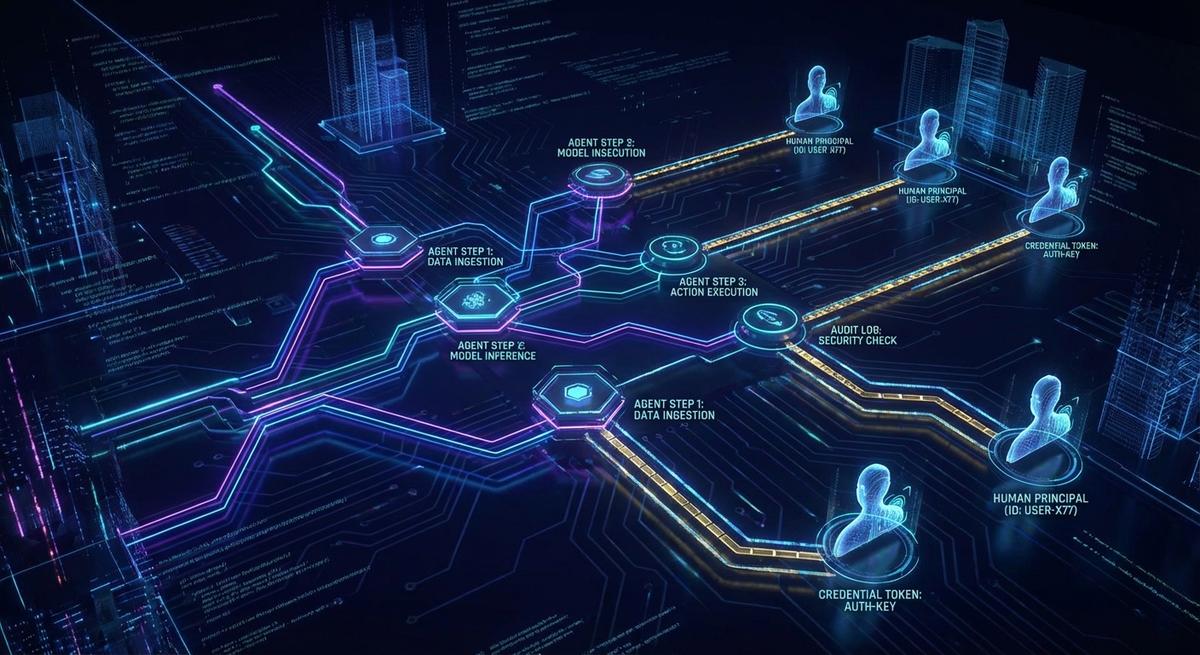
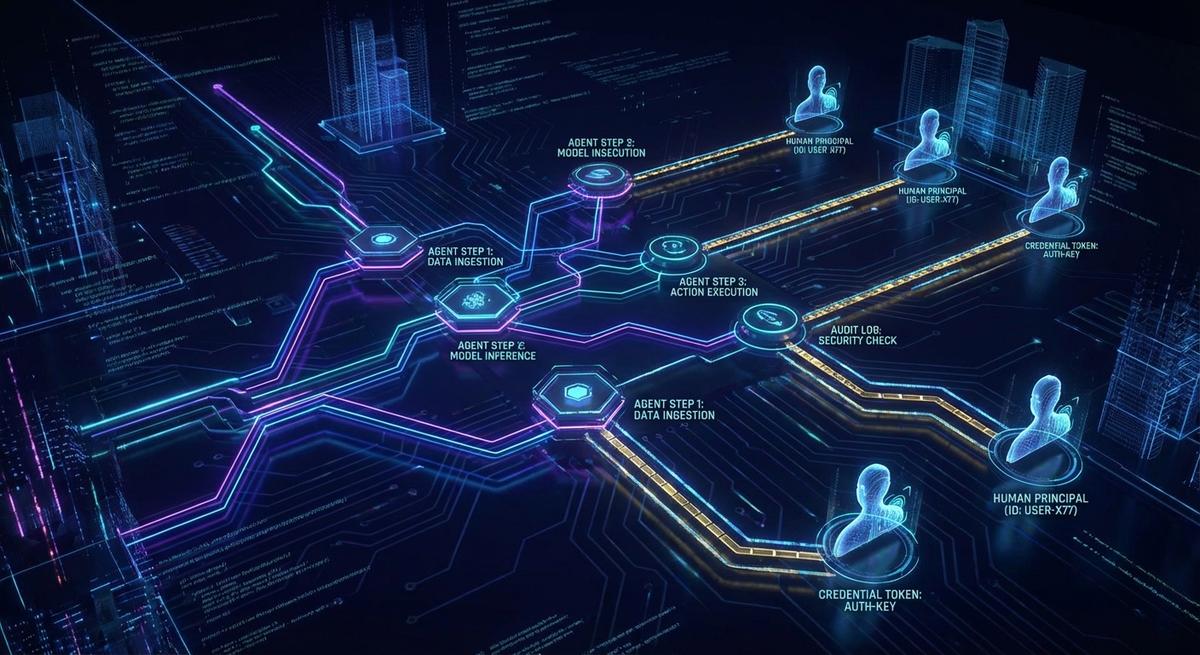
AI agents execute across tools with no memory of what came before. Your logs capture 200 OKs, not consequences. Here's how to build workflow-level audit trails that actually show what happened.
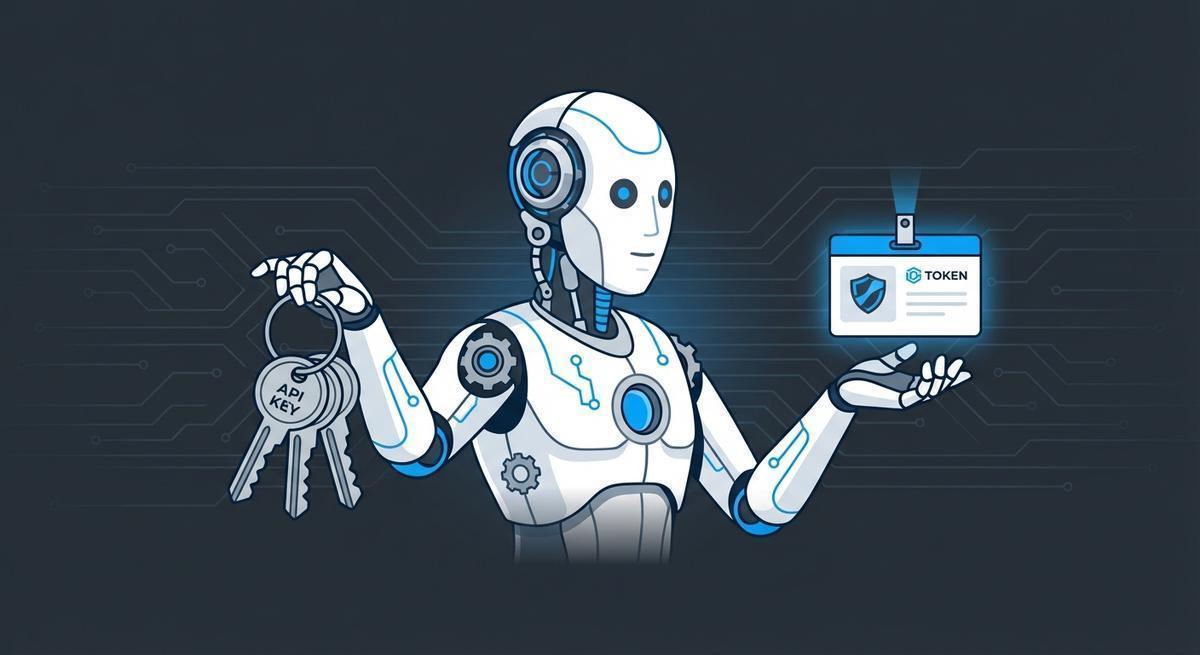
Long-lived credentials in `.env` files aren't a best practice; they're a countdown timer. Workload identity gives agents short-lived tokens that expire before they can do damage.
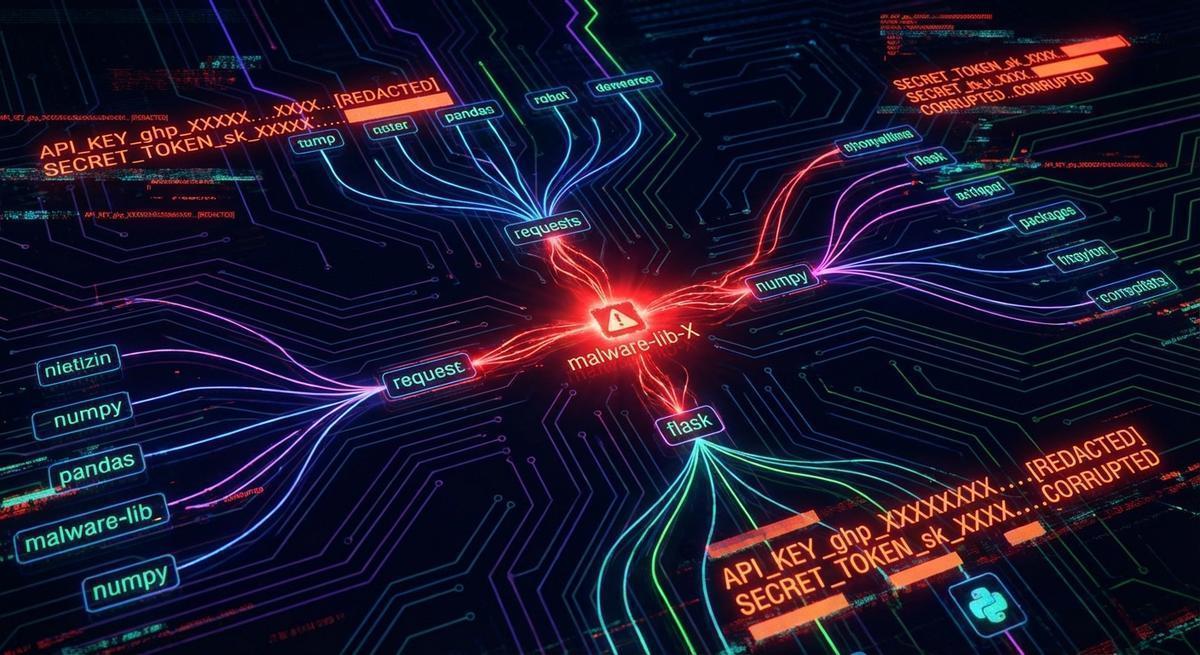
The LiteLLM 1.82.7 backdoor drained API keys before most teams could rotate. Phantom tokens make stolen credentials worthless by design.
When AI agents go wrong, everyone blames the model. They're wrong. A forensic look at real incidents shows the same credential architecture failure, every time.

When multiple AI agents share the same credentials, one compromised agent exposes everything. Here's how to give each agent its own isolated session with the exact keys it needs.

A practical pre-deployment security checklist for AI agents. Catch credential leaks, over-permissioned keys, and blast radius risks before they hit production.

Stop hardcoding API keys into MCP servers. Here's the register→scope→issue→validate→expire pattern with real endpoints platform engineers can deploy today.