Your AI Agent's API Key Will Leak. Here's the Fix.
Long-lived credentials in `.env` files aren't a best practice; they're a countdown timer. Workload identity gives agents short-lived tokens that expire before they can do damage.
Practical security insights and product updates from the team building safer, simpler key management for modern APIs.

MCP skill marketplaces have the same supply chain problems as npm, except the blast radius is your AI agent's full context window. Here are 5 vulnerabilities with code fixes you can deploy today.
Read →
Your secrets management provider can read your plaintext API keys. Here's how zero-knowledge encryption works, what it changes for compliance, and when enterprise teams actually need it.
Read →
API keys shared through Slack, email, and spreadsheets waste developer hours and create security gaps. Here's what insecure credential sharing actually costs your team, and how to fix it with automated, encrypted sharing.
Read →
Long-lived credentials in `.env` files aren't a best practice; they're a countdown timer. Workload identity gives agents short-lived tokens that expire before they can do damage.
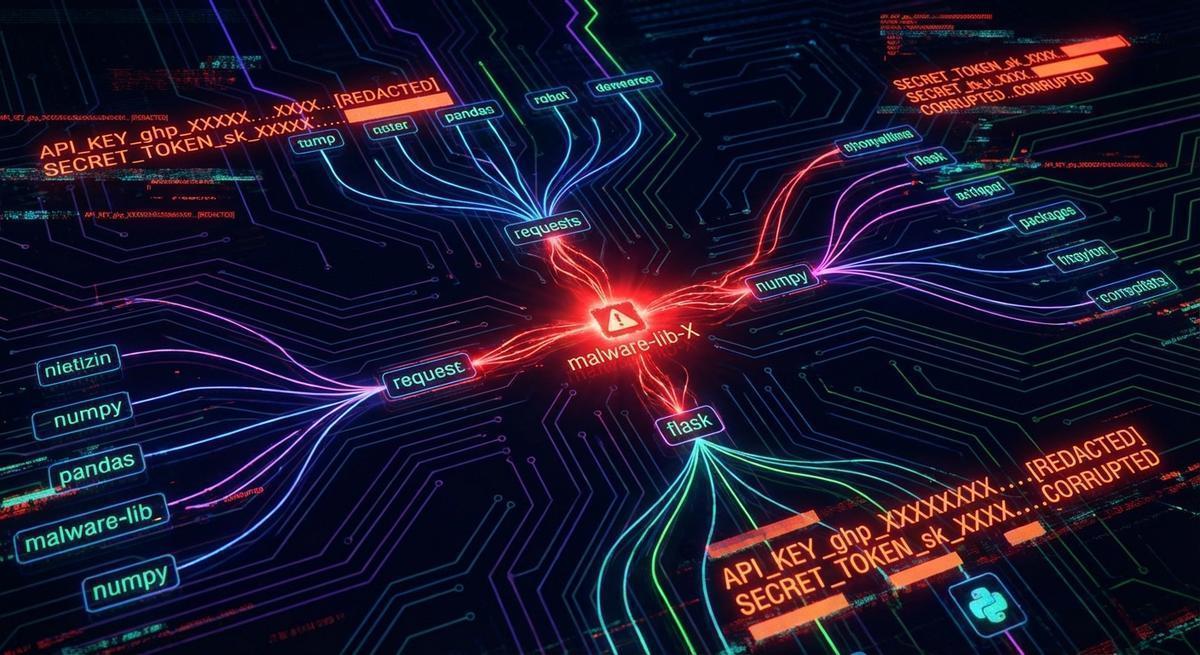
The LiteLLM 1.82.7 backdoor drained API keys before most teams could rotate. Phantom tokens make stolen credentials worthless by design.
Localhost phantom tokens give you a false sense of security. Production environments break the pattern in 4 specific ways. Here's the 3-command setup that actually holds up.

A ClawHub skill runs with the same permissions as your OpenClaw agent, no sandbox, no isolation. Here's what you should check before installing any third-party skill.
When AI agents go wrong, everyone blames the model. They're wrong. A forensic look at real incidents shows the same credential architecture failure, every time.

Tool poisoning bypasses credential security entirely by corrupting your agent's tool calls at runtime. No stolen keys, no breach alerts, just your agent doing exactly what an attacker wants.
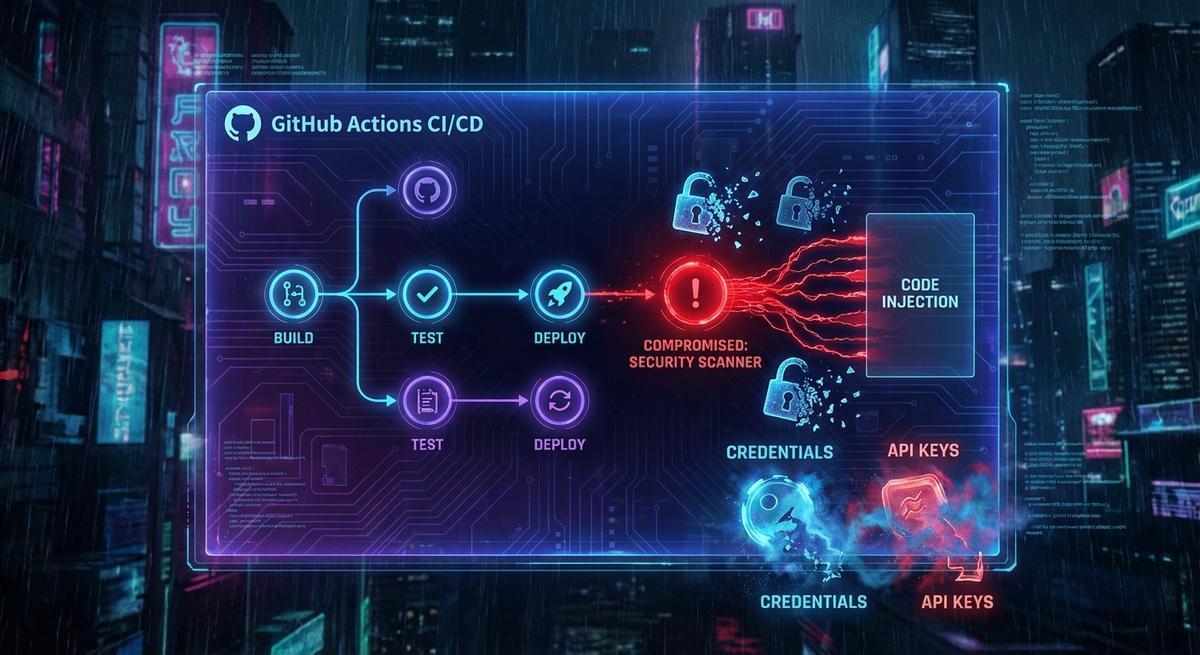
The Trivy action attack exfiltrated AWS keys, GitHub tokens, and SSH credentials from pinned pipelines. Pinning fixes one vector. Scoped, ephemeral secrets fix the problem.

The Trivy supply chain attack proved it: static secrets in GitHub Actions are sitting ducks. Here's how to replace them with ephemeral, scoped credentials that auto-expire in minutes.
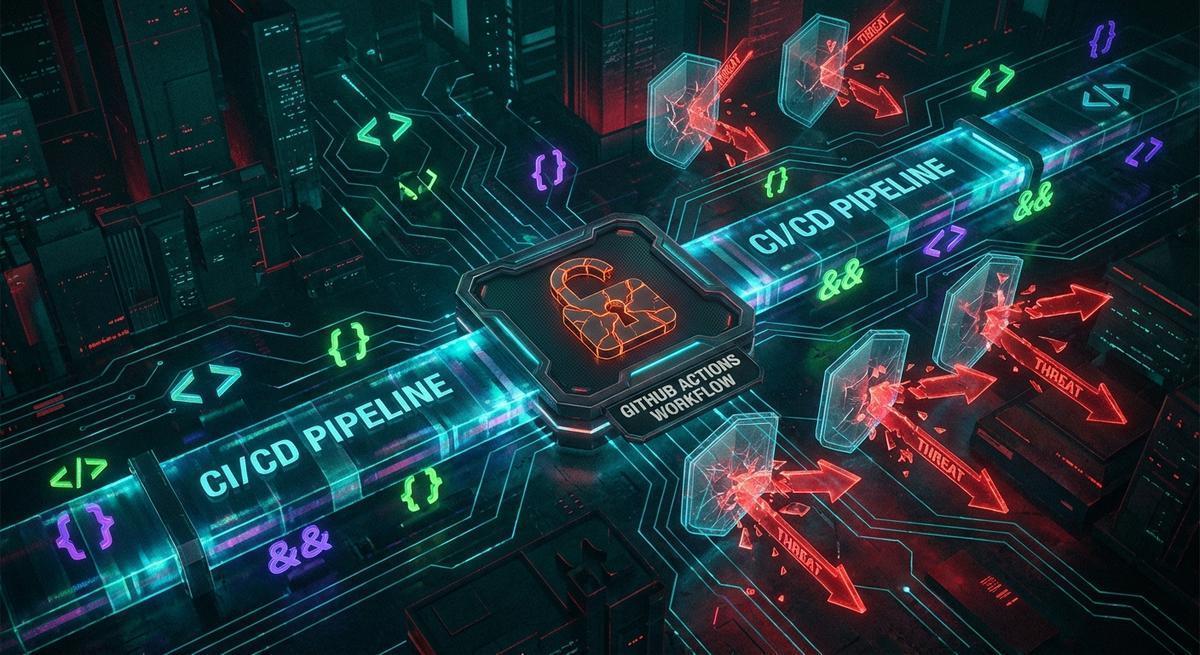
Attackers hijacked 75 Trivy GitHub Action tags without finding a single vulnerability in your code. They targeted the secrets you left in CI env vars, and thousands of pipelines handed them over.
We run AI agents in production that handle Telegram, GitHub, Reddit, and HN integrations. Here's exactly how we use API Stronghold to keep credentials out of agent context.